AI Assistants: Are they making your code less secure?
Everything I do professionally is around helping engineers create amazing applications that are both secure and reliable. That’s why I build engineering tools and educational content that simplify application security.
Throughout my career, I have performed security audits for private and open-source projects, and have found critical vulnerabilities in Google and Mozilla products. I have also taught security to hundreds of engineers and students, while I have also been an external lecturer and Ph.D. candidate in computer science at the Technical University of Denmark.
Here are some of the things I’m working on right now:
- Developing a tool 🛠️ that helps software engineers build applications which comply with privacy requirements
- Creating weekly educational content on application security using comic art 🦇
- Creating a blog 📝 on security at securingbits.com
If you’re interested in learning more about application security, I’d love to hear from you. Feel free to send me a message, and make sure to follow me so I can make security easy for you 🙂
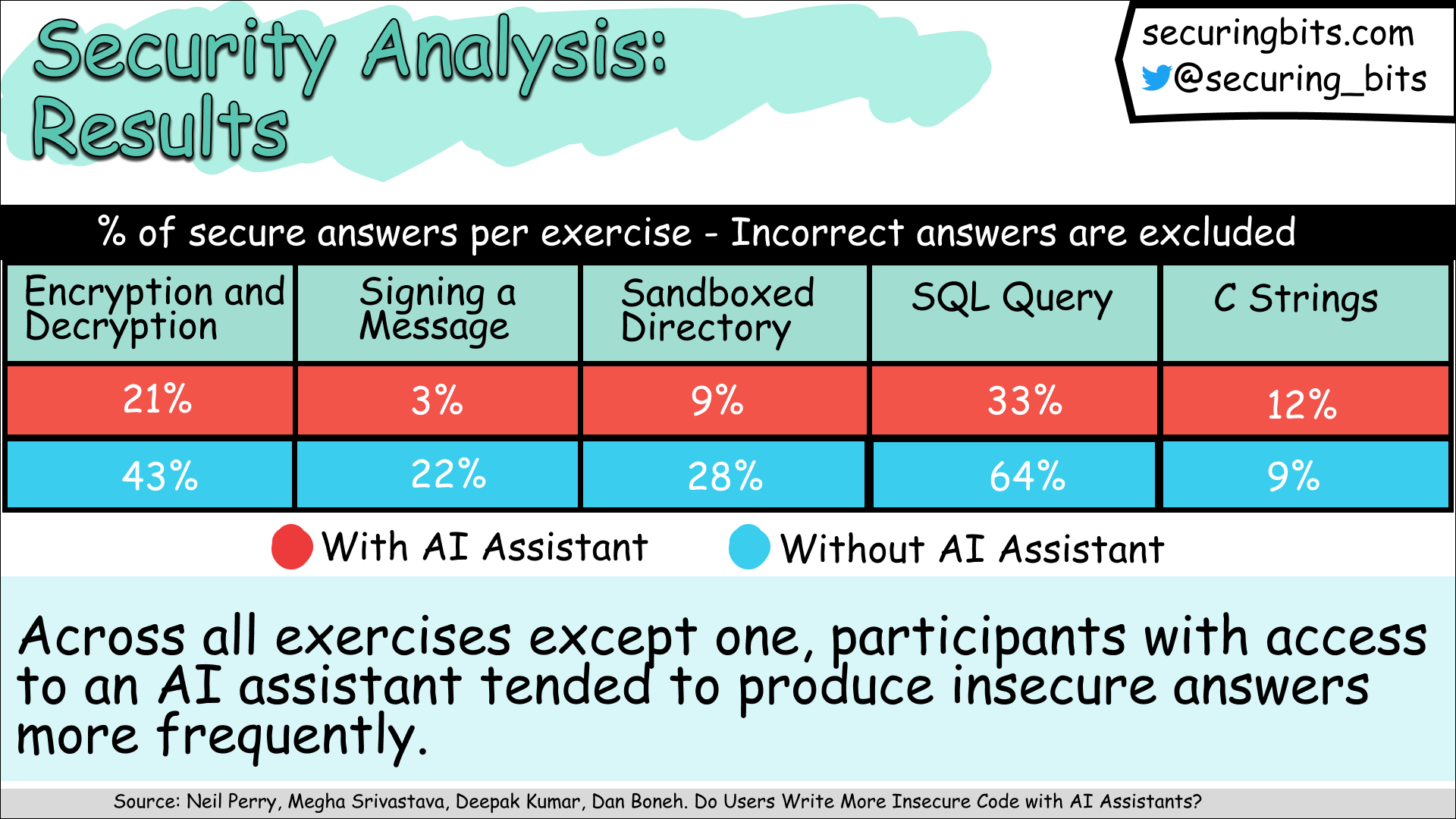
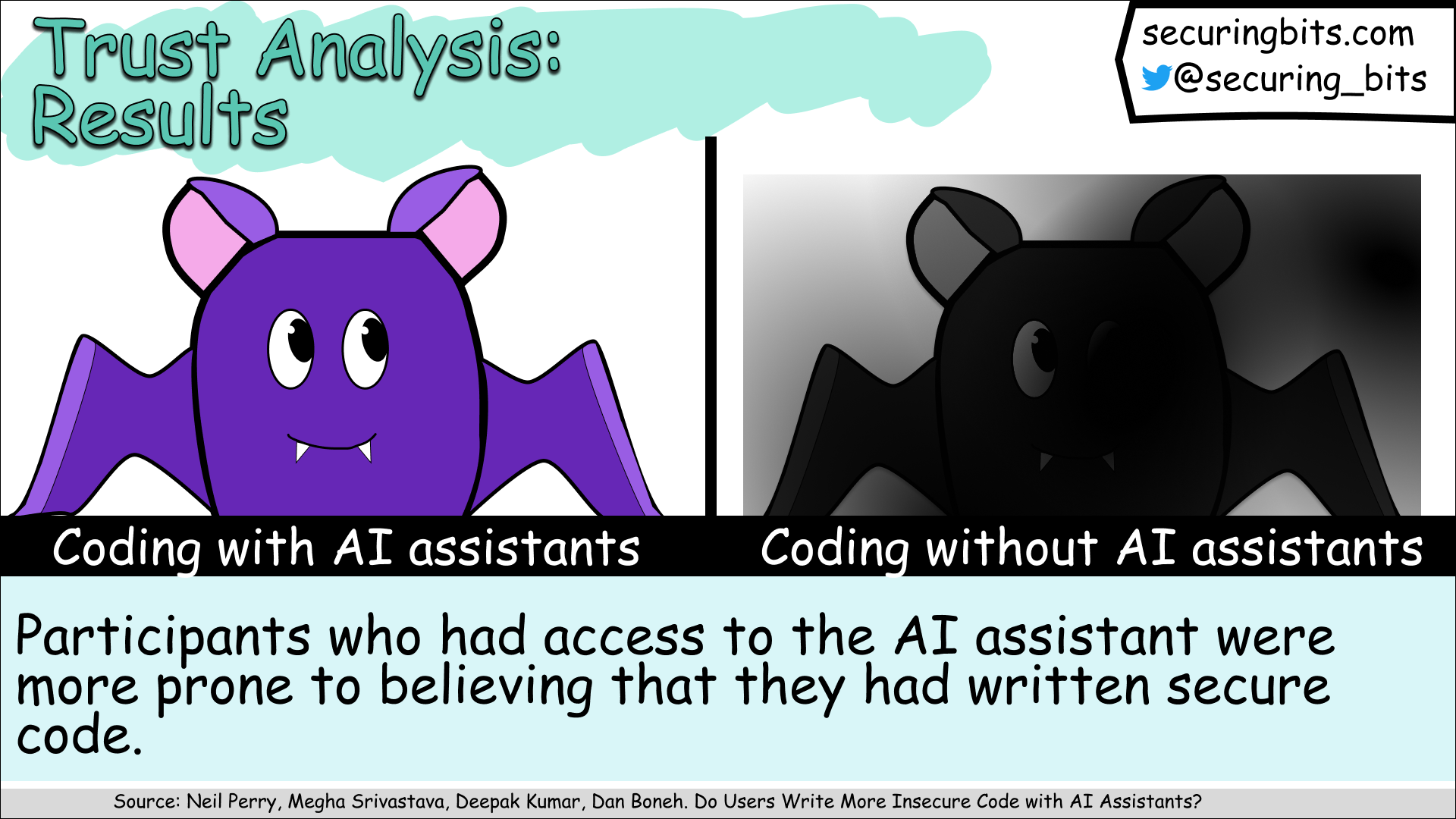
AI assistants can write code, offer suggestions, and streamline our work. But here's the million-dollar question: Can they make us write less secure code?
Today's comic will give you three insightful results on this topic. 🙂
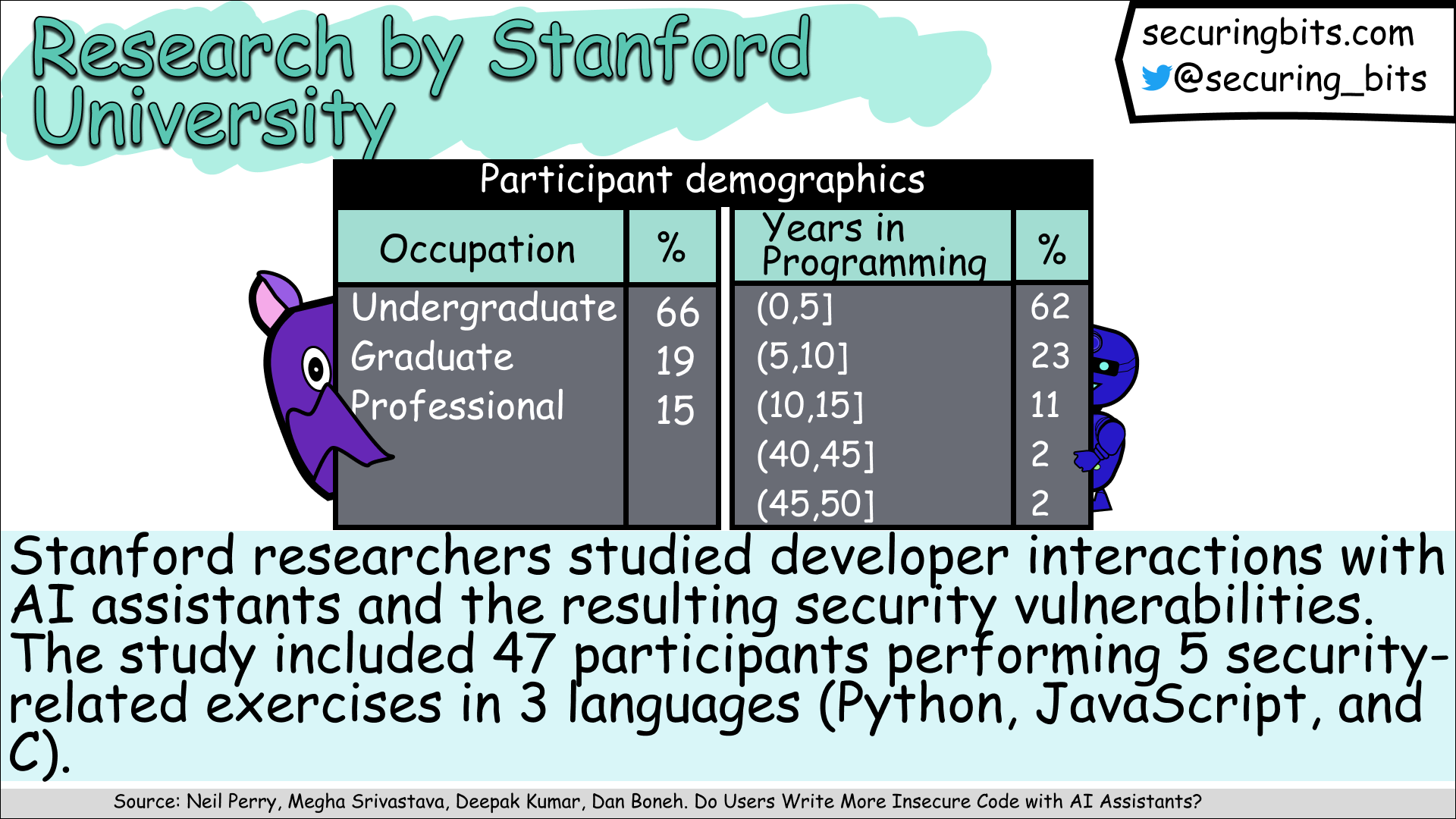
Those results are based on the paper "Do Users Write More Insecure Code with AI Assistants?" written by Stanford Researchers: Neil Perry (https://lnkd.in/e_y9ThrY), Megha Srivastava (https://lnkd.in/eJrTwdDC), Deepak Kumar (https://lnkd.in/ekizARJX), and Dan Boneh (https://lnkd.in/ePGAKGxM). You can find the full paper here: https://lnkd.in/eukMWQiz.
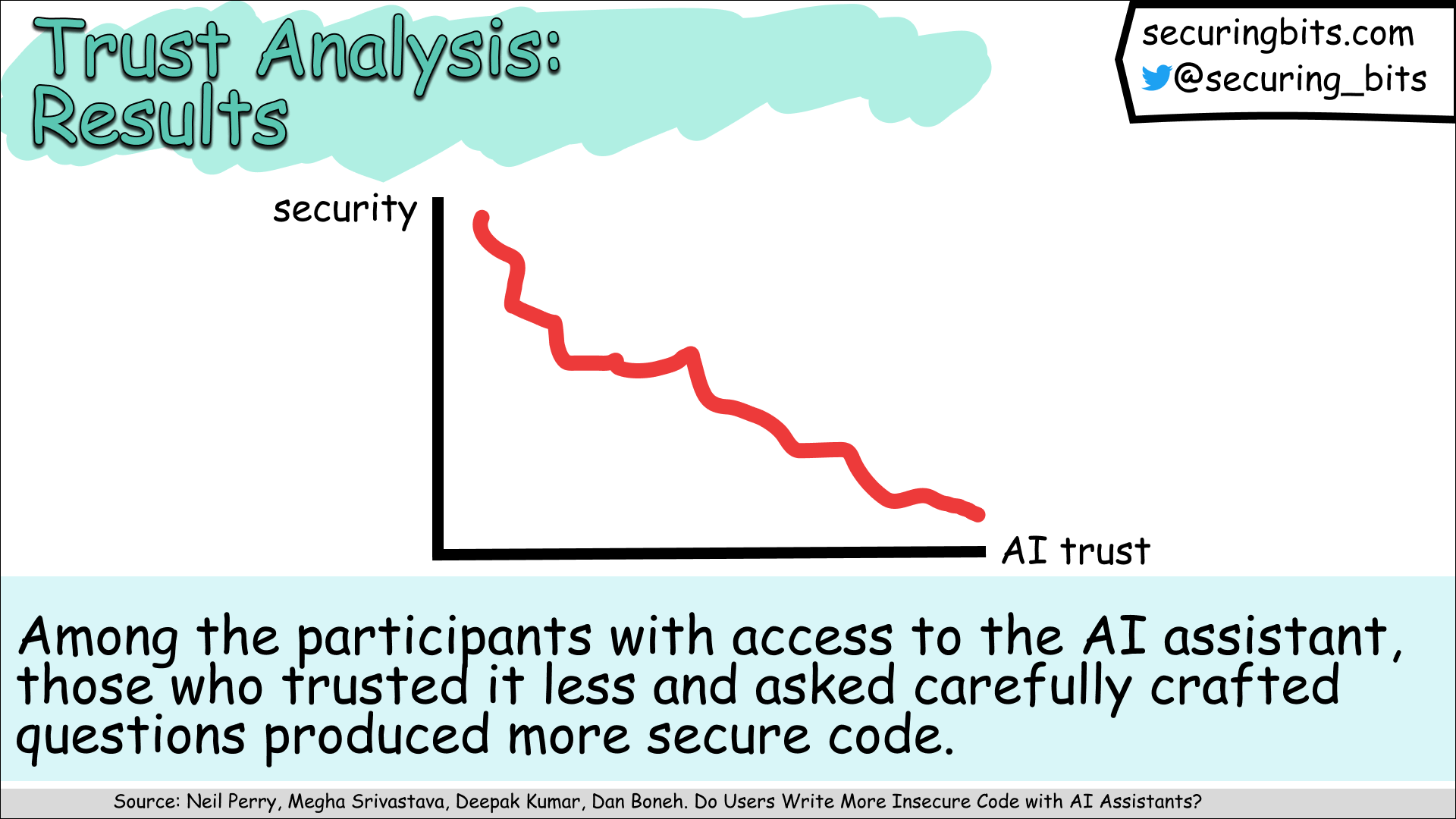
I believe that future AI assistants will provide numerous benefits for software engineers. However, at least for now, the quality of their output greatly depends on our input and interactions with them.